This is the third article in a series of articles covering VPN in Windows Essentials. In the first article I covered an issue with VPN and DHCP. In the second article I covered how to re-deploy VPN with PowerShell in 2016 Essentials. In this article I will cover how to re-deploy VPN in legacy mode.
- First we must clear the configuration. Launch a PowerShell session as administrator.
- Run Uninstall-RemoteAccess. Hit enter when prompted.
- Install the RRAS (Routing and Remote Access Service) console by running the following command: Install-WindowsFeature RSAT-RemoteAccess-Mgmt
- Run rrasmgmt.msc to launch the RRAS console.
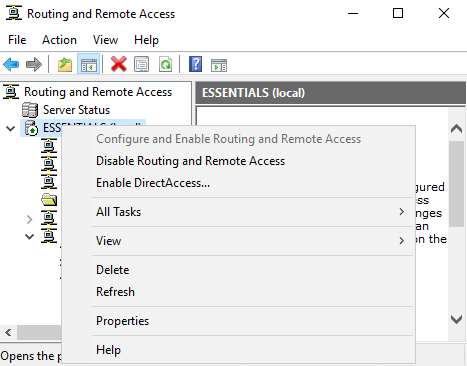
- Right-click on the server name and choose “Configure and Enable Routing and Remote Access”

- Click Next.
- Ensure the Custom configuration radio button is selected and click Next.

- Check the box for VPN and click Next.

- Click Finish to complete the initial configuration. You will get a popup indicating a policy was created. Click OK to continue.

- When prompted to start the service, click Start service.
- RRAS is now running, but there are two more required steps to complete the configuration. Right-click the server name and choose Properties.
- Click on the Security tab. At the bottom of the screen, choose the correct certificate and click Apply. Click Yes to restart RRAS.

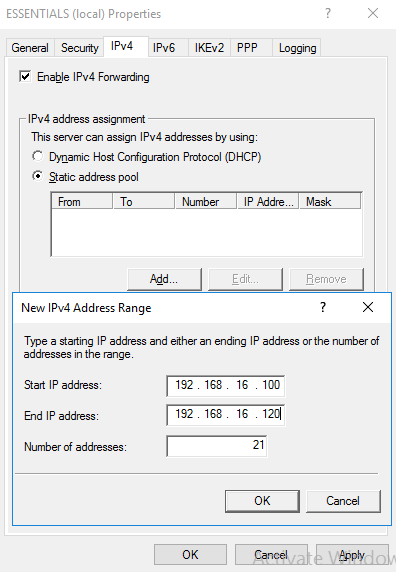
- Click the IPv4 tab. Click the radio button for Static address pool and click the Add button. Fill in the start IP address and end IP address and click OK twice.
- Restart the RRAS service.
At this point RRAS should be configured properly. Optionally you can disable the unused protocols in RRAS. To do so right-click on Ports and click Properties.

Only SSTP is used in Essentials by default, so the other protocols can be removed/minimized. Highlight IKEv2 and click Configure. Change the maximum ports to 0 (zero) and click OK. Click Yes on the popup. Repeat this with L2TP and GRE. For PPTP you cannot reduce to zero, but you can reduce to 1 (one). I also like to reduce the number of ports to match the number of IP addresses in the static pool. This is to ensure that all connections get a valid IP address. So I limited the ports to 20 for SSTP. When complete it should look something like below.

I hope you found this article informative. If you have anything to add or just want to comment, please do so below.
Very useful instructions! thanx
LikeLike
I really love this kind of tutorials it’s really informative and easy to follow because of the step by step images. I also just want to share this list of free VPNs for those who want to try it: https://vpnalert.com/best-virtual-private-network/free/
LikeLike
When I reach the end of routing and remote access server setup wizard, an error dialog appears:
Installation of the Routing and Remote Access service failed because:
Class not registered
(80040154)
When the expected behavior is to notify that is has created the default connection request. All the previous steps worked as expected. This is Server essentials 2016, patched up to date.
LikeLike
It is possible your WMI repository has issues. I would try a reset with the following command: winmgmt /resetrepository
LikeLike
Does this disable the AnywhereAccess configuration through the dashboard?
Thanks
LikeLike
No, this is completely separate from the Anywhere Access wizard. However if you run the Anywhere Access wizard again it will reset the configuration for VPN.
LikeLike
This worked perfectly apart from having to restart the server after reconfiguring it. Before I restarted it I could connect fine but not ping any remote IP addresses.
Thank you.
LikeLike
Have you tried to deploy DUO with the Essentials Role installed? I would like to protect VPN AND the Remote Web Workplace / Anywhere Access features with MFA/DUO. Any tips? Seems like NPS gets in the way. Also DUO seems to require PAP. When enabled in NPS then RRAS service won’t load…. Anyway, just asking. It would be a super helpful tutorial (according to me). =) Thanks for the above though; very informative..
LikeLike