Here is a situation I run into on a frequent basis.
- We have a new server from a OEM (Original Equipment Manufacturer) like Dell, HP or Lenovo.
- The server has a factory installed OEM operating system.
- The server is setup as a Hyper-V host with virtual machines
- The user setting up the virtual machines does not have physical access to the server.
- The user extracts the product key from the host with a tool like Belarc advisor or Magical jellybean keyfinder.
- The user attempts to use the extracted product key on the virtual machines and activation is not successful.
So where did the user go wrong in the above situation? And if the product key works on the Hyper-V host, why will it not work on the virtual machines?
Before we can answer the above questions we need to understand a little about the type of product key used by large OEMs. Typically when a Windows operating system is installed by an OEM, an OEM_SLP (System Locked Pre-installation) key is used. This type of key is used to save time when building servers, as the server does not have to be activated with Microsoft. When this type of key is entered into a Windows installation, Windows will query the SLIC (System Licensed Internal Code) table located in the BIOS (Basic Input Output System) of the machine. If the table matches what is expected, then Windows will activate. With this in mind, a Dell OEM SLP product key can only be used on a Dell server. And an HP OEM SLP product key can only be used on a HP server.
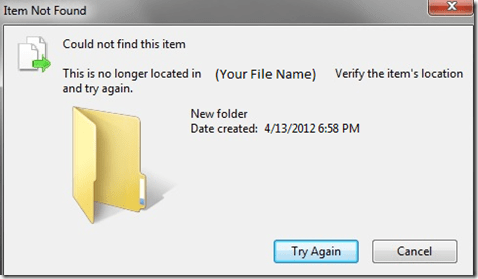
To answer both questions. As explained above the product key in the Hyper-V host is an OEM_SLP key. This key requires that Windows query the bios of the system and verify the SLIC table matches. A virtual machine has an emulated bios from Hyper-V. The SLIC table does not match and Windows will not activate.
Now that we understand the problem, how can we identify it.
- A couple of questions to start with. Did the server come pre-installed with Windows. If so, has the product key been changed? If the server came pre-installed with Windows and the product key has not been changed, then we likely have an OEM_SLP product key.
- On the Hyper-V host and the virtual machine, do the following.
- Open an administrative command prompt
- run the following command: slmgr /dlv If the Product Key Channel is OEM:SLP, then you have confirmed we have an OEM:SLP product key

The solution is quite simple. The user needs to locate the product key sticker on the server and use the product key from it to activate the virtual machines. Here are the commands to run, from an administrative command prompt, on the virtual machine to do this quickly:
- slmgr /upk
- slmgr /ipk xxxxx-xxxxx-xxxxx-xxxxx-xxxxx (replace the x’s with the actual key)
Windows should then activate within a minute.