Good morning. I had a question today on what to do if the hard drives are not detected when performing a bare metal restore. Loading the driver is pretty straightforward, but I could not find a good guide on the whole process, so I figured it was time to put one together. Below I will outline with screenshots the process to do a bare metal restore. The screenshots will be from Windows Server 2016, but the process is the same for all currently supported versions of Windows.
- We start by booting to the Windows media. After selecting the language, you have two options; Install now or Repair your computer. Choose Repair your computer.

- The next screen may give you more or fewer options. Choose Troubleshoot.

- From the Advanced options screen, choose System Image Recovery.

- If given the option for a target operating system, choose the one applicable to you.

- On the following screen, you will have two options; Use the latest image or select a system image. If you want to restore the latest backup, then you simply need to click next. If however you want to restore an earlier backup, choose the option to select a system image. This guide will continue with the second option.

- If you have only one backup drive, then only one line item will show. A line for each backup drive will be displayed on this screen. Choose the backup drive to restore from and click Next.

- On this screen all the available backups are displayed to restore from. Select the preferred backup to restore and click Next.

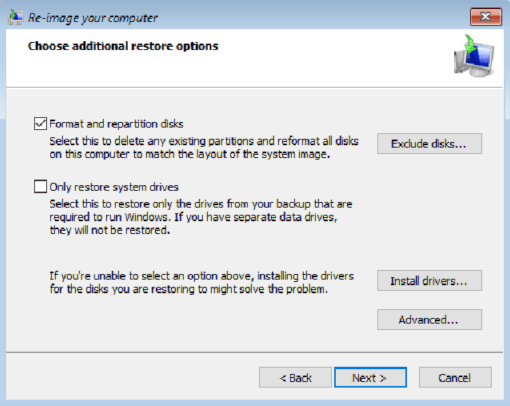
- This screen provides three important options. The first is to format and repartition the disks. Select this option to completely wipe the drive being restored to. It is possible to exclude data drives from this by clicking the exclude drives button and checking the drive to exclude. The second option will only restore the system drives. Keep in mind though, if the page file was moved a data drive, that drive is now considered a system drive and has to be part of the restore. The last option is to install drivers. Do this if the drives being restored to are not detected by the restore wizard. Once all desired options are selected, click Next.
- This screen is a summary of the restore. Click Finish to start the restore process.

After clicking yes on the prompt, the rest of the process is automated. The server will be restored and automatically boot back into the restored Windows OS.
I hope you found this post informative. If you have anything to add or suggest, please do so in the comments below.