Good afternoon. Longtime readers of this blog likely figured out that I work quite a bit with Essentials. I wanted to take a few minutes to go over the changes good and bad and my views on why we see are seeing them. I have heard a lot of grumbling over the removal of some features. This article will attempt to take a more unbiased review of the situation. Just a couple disclaimers first though. I do not work for Microsoft and my views here are my own.
Let’s tackle the elephant in the room first. The removal of the essentials experience. This includes the dashboard, connector software, remote web access and client PC backup. Based on my interactions, most people I talk to see this in a negative light. I tend to view this as business as usual.
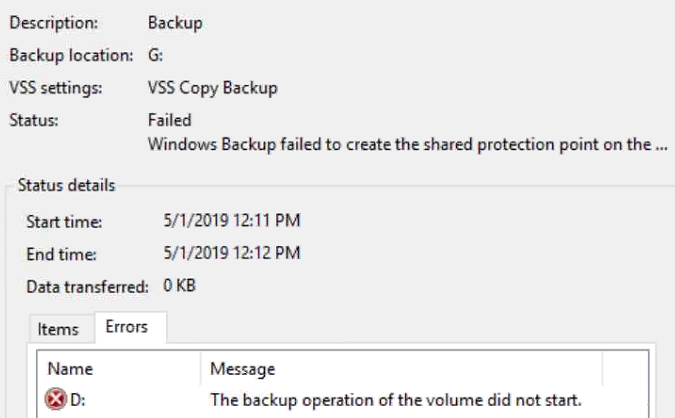
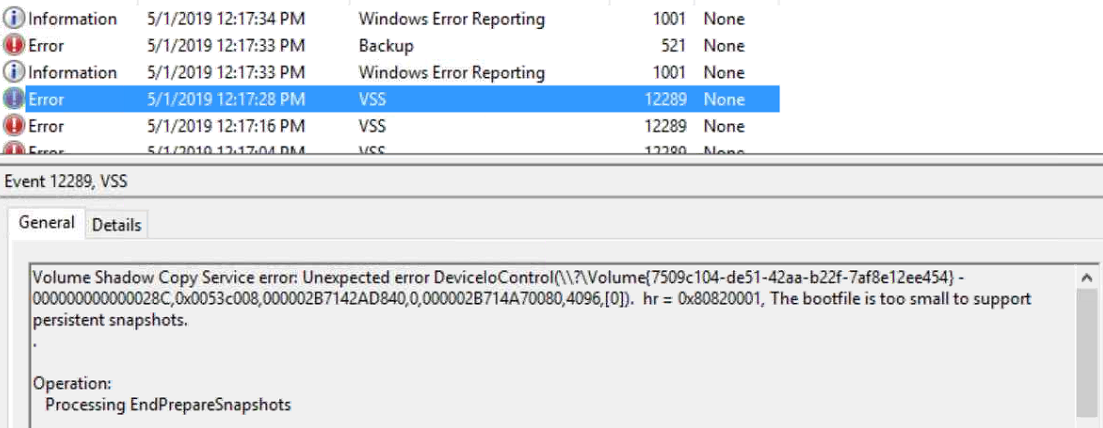
I say this as I have been supporting Microsoft small business products for about 15 years now. I started out supporting SBS 2003. I watched that product mature into SBS 2008 and then peak with SBS 2011. Unfortunately due to the all interactions between the different software packages, SharePoint, Exchange, Active Directory, etc… it meant that putting out SBS 2014 was not going to happen. This is why I believe Microsoft decided to re-badge Windows Home Server as Windows Server Essentials edition. The product was changed some, but when first released was about 98% the same. Windows Server Essentials then matured into Essentials 2012, then 2012 R2 and finally peaked with 2016. While Essentials has been great in the past, the number of issues has been steadily creeping up. There are two that I believe contributed to the demise of Essentials. The first is the client PC backup feature. This feature, while great for a few workstations, does not scale well. The second problem though is likely a bigger part of why the Essentials experience was removed. Within the last few years the client connector software has become more troublesome to maintain. This seems likely due to the change in how updates are packaged for Windows 10. I have seen many workstations that required a reinstall of the connector software after an update. It’s not all bad though. I have seen quite a few Essentials environments that have been working great. These environments tend to run Windows 7 for the workstations, and have fewer than 10 workstations and/or users.
So were the building problems the only reason that the essentials experience was removed? I don’t think so. There is a lot of grumbling that Microsoft has removed the essentials experience to drive more customers to their hosted services. While there is likely some truth to this, I don’t believe it is the primary reason. It is more likely that the segment of the market that the essentials experience serves has shrunk to the point it is no longer profitable to continue development and support of the product. If it were, then Microsoft would devote more resources to the problems with the essentials experience.
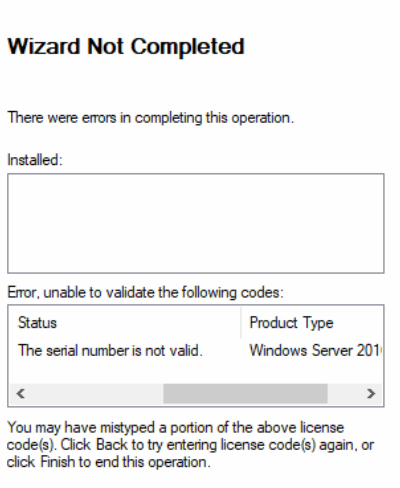
So I like to consider myself an optimist and look at the bright side. There is definitely a silver lining here if you look closely. Through testing of Windows Server 2019 Essentials edition I have found several positive points. The first is the removal quite a few of the restrictions placed on previous Essentials editions. It is no longer a hard requirement to have an Active Directory domain in place. The licensing compliance checks will pass without problems if the server is left in a workgroup. This is a huge win for a lot of small businesses as it brings down the IT cost of maintaining and setting up a server. The server can simply be managed as a workstation would be. Another positive is that CALs (Client Access Licenses) are still included with the Essentials edition. While the 25 user limit is still in place, all 25 users are licensed without additional cost. Finally the cost of Essentials edition has remained largely unchanged. For less than half the cost Standard edition you get a server class OS with 95% of the features and very few restrictions*.
I hope you have found this informative. If you have an opinion on the subject or have another viewpoint please feel free to comment below.
*Remote Desktop Services and Data Deduplication have been removed from Windows Server 2019 Essentials edition. This is not really a change from 2016 Essentials edition as Remote Desktop Services, while there, did not function properly.