Good morning. I had a case yesterday that yielded several interesting article ideas. This is probably the most interesting one, and I have seen this very issue on at least three occasions. The issue started on a domain rename. If you have ever done a domain rename, you know there are quite a few steps. After doing some checks and making some corrections we were able to complete the domain rename. My customer then advised that his Folder Redirection policy was not applying on any workstations. So in this article I am going to cover how to troubleshoot a group policy not applying and the specific fix for the situation I ran into yesterday.
The first step when troubleshooting just about any group policy issue is to pull a group policy report from a client that should be getting the policy. My preferred method is to go to a command prompt and run the following commands:
gpresult /h report.htm
report.htm
This will run the report and save it to a file called report.htm. The second line then opens that report in a web browser.
When troubleshooting an issue where a policy is not applying I like to focus on the denied sections. In our case folder redirection is a user policy, so I checked there. Below is similar to what I found.

There were two clues as to what the issue was here. The first clue is that the policy name is not being displayed. Instead we just see the GUID (Globally Unique Identifier). The second clue is the reason denied. We can see it was denied because the policy is inaccessible, empty or disabled.
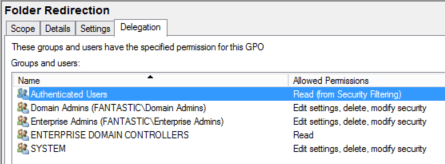
The next step was to check to see if the policy was accessible in the SYSVOL share. In our case we had no problem accessing the files. We then checked in the group policy management console. We verified the policy was not empty or disabled. So it would appear that we have eliminated all possible issues. However there is another set of permissions.
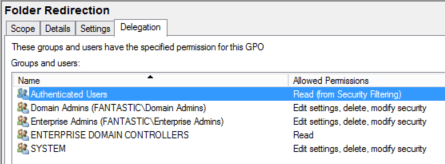
This was the set of permissions that were not correct in our case. The Authenticated Users group was missing. I have seen this issue on several occasions when one of my customers is trying to “lock down” the server. Even if you add in another group, for instance Domain Users, and the user and/or computer is a member of that group, the GPO (Group Policy Object) will still fail to apply. The fix is quite simple. Add back the Authenticated Users group and give it read permissions. After adding back Authenticated Users and running a gpupdate /force on the client the policy applied without issue.
I hope you have found this informative. If you have anything to add or just want to comment, please do so below.