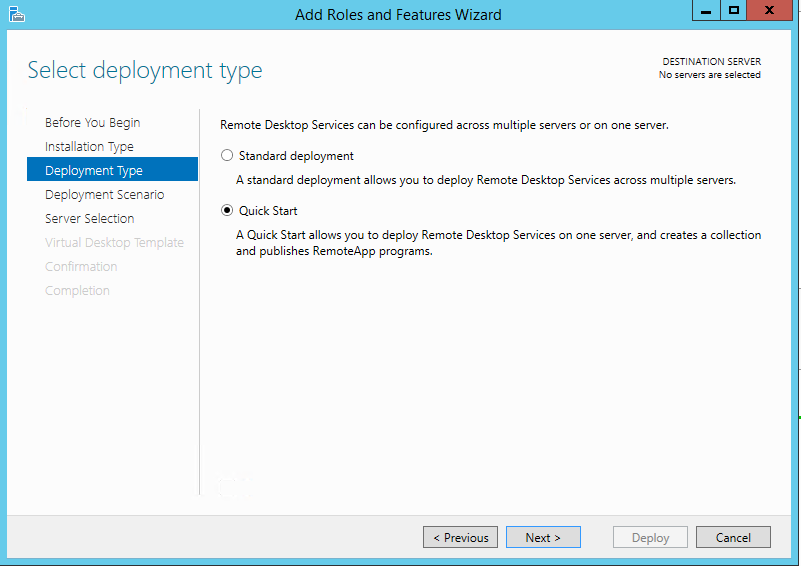
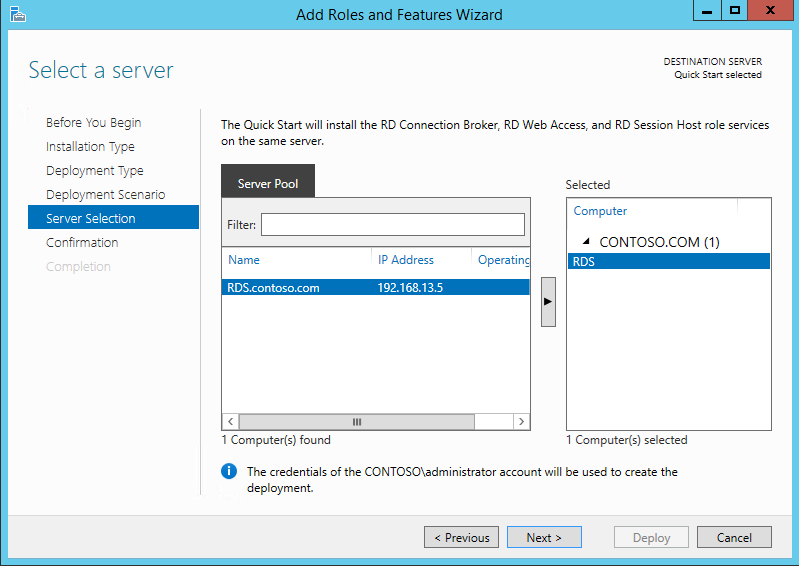
I have previously written an article on setting up RDS (Remote Desktop Services) in domain environment. However, what if there is only one server and/or there is no domain? It is still possible to setup RDS, but the process is a little different. Connection broker, a component of RDS, does not work properly in a workgroup environment. Also it is not possible to use Remote App, another component of RDS, or create a session collection. Without a session collection, Session Host, yet another RDS component, will not be able to obtain licenses. Without licenses RDS will cease to function after the initial grace period. Typically this is 120 days. We get around this by manually editing the WMI attributes for Session Host.
Here is how to properly deploy RDS in a workgroup. I am going to use PowerShell to make this quick and easy. This guide is applicable for Windows 2012, 2012R2 and 2016 in a single server workgroup environment. If you have Windows Server 2019 or higher the process has changed. Skip to the bottom for that process.
- Launch a Windows PowerShell using the Run as Administrator option.
- Run the following command to install the RDS components that are required. (This will automatically restart the server)
Install-WindowsFeature RDS-RD-Server,RDS-Licensing -IncludeManagementTools -Restart - After the server restarts, log back in.
- Launch a Windows PowerShell using the Run as Administrator option.
- Run the following commands to manually configure Session Host*.
- $obj = gwmi -namespace “Root/CIMV2/TerminalServices” Win32_TerminalServiceSetting
- $obj.ChangeMode(2)
- $obj.SetSpecifiedLicenseServerList($env:computername)
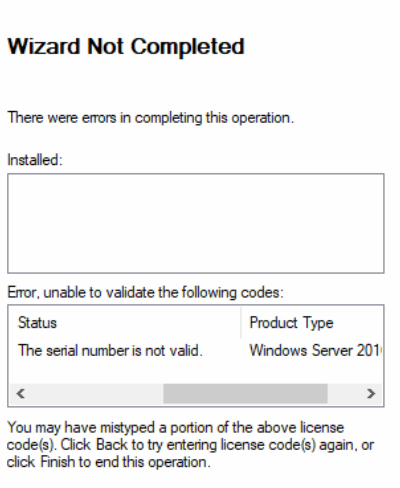
The next step is to activate the RDS license server and install RDS CALs. You can find an article on how to do that here.
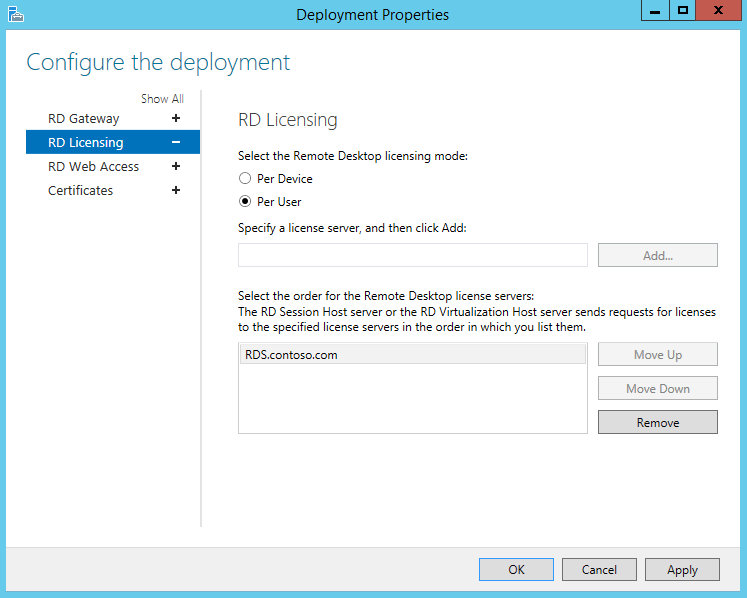
* On the $obj.ChangeMode() command:
$obj.ChangeMode(4) = Per User licensing
$obj.ChangeMode(2) = Per Device licensing (supported mode for workgroups)
An update to this article. It appears in Windows Server 2016 and 2019 Microsoft is enforcing Per Device mode in a workgroup configuration. So if you install RDS in a workgroup in 2016 or 2019, you should use Per Device mode. This is not usually an issue as RDS CALs can be converted between Per User and Per Device in the licensing manager.
Another update, July 2021. Microsoft has changed the process for Windows Server 2019. The above PowerShell script will fail to set the mode. To properly do this the registry needs to be edited.
- Open Registry editor (Right-click Windows logo at the bottom left and choose Run. Type regedit and hit enter.)
- Navigate to:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server\RCM\Licensing Core
- Verify there is a DWORD for “LicensingMode” and it is set to 2. If not present, right-click and choose New-> DWORD (32-bit) Value. This must be set to 2 for “Per Device”
- Navigate to:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\TermService\Parameters\LicenseServers
- Verify there is a Multi-String for “SpecifiedLicenseServers” and it is set to the server’s name. If not preset, right-click and choose New->Multi-String Value.
- Reboot the server.